On Saturday, Belt Finance suffered a flash loan attack, following a series of exploits against DeFi protocols on the Binance Smart Chain.
1/8
New weekend – a new attack on BSC DeFi protocol.
Today $6.2M in BUSD was stolen from Belt Finance in 8 transactions.
Below is what happened👇 pic.twitter.com/1URb9sJud0
— Igor Igamberdiev (@FrankResearcher) May 29, 2021
6 Millions for Attacker Spell 50 Millions lost
According to a blog post by Belt Finance, the attack was carried out on the BSC 4Belt yield farming pool that accepts deposits in USDT, USDC, BUSD, and DAI. Following a very sophisticated exploit, the attacker then took off with a profit of 6.23 million USD.
However, the attacker’s profit does not take into account the overhead cost accrued in gas fees. In total Belt Finance estimates the total damage suffered by investors into the yield farming pool to total 50 million USD.
Attacker exploits complex Loophole in Yield Farming Strategy
Using flash loans (uncollateralized DeFi loans that are paid back within the same block), it is possible to create sophisticated attack vectors that exploit the complex structure of DeFi smart contracts.
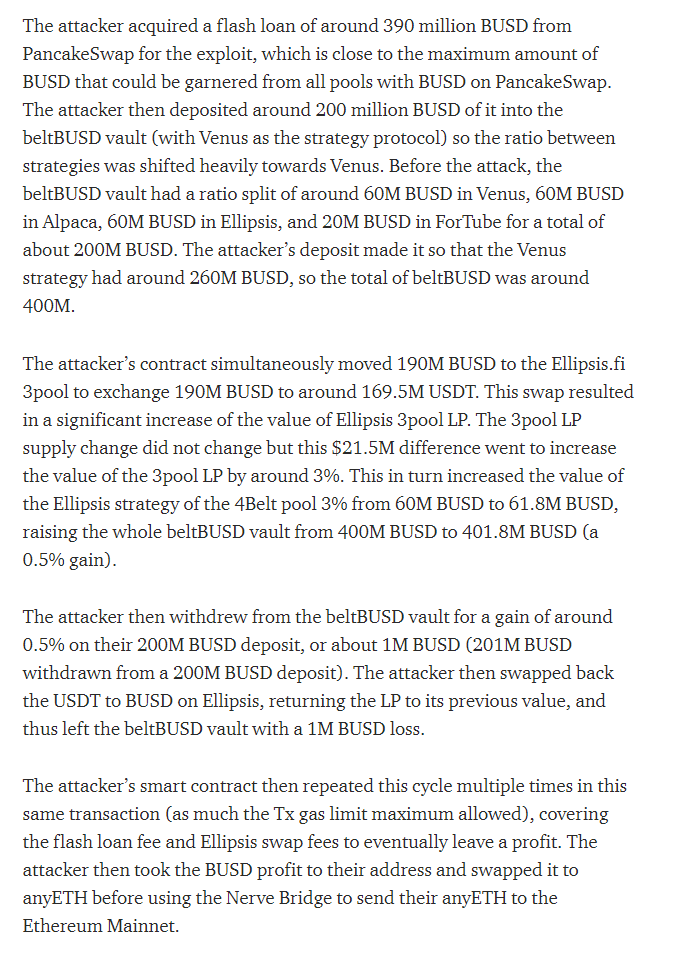
According to Belt Finance, the attacker in the most recent smart contract hack executed on the Binance Smart Chain took out a flash loan worth 390 million BUSD on PancakeSwap, using a total of eight trading pairs. This made it possible to change the yield farming strategy in Belt’s deposit pools to the attacker’s favor, through several third-party DeFi platforms:
As of now, Belt Finance has suspended all deposits and withdrawals, expecting full functionality to be regained within 48 hours. On their Twitter account, Belt announced that they have patched the faulty smart contracts, with an external audit pending. Additionally, the yield farming platform wants to come up with a plan to compensate the investors affected by the incident.
5/ We are also in the process of creating a compensation plan for our users. Our users and their assets are important to us, and while this attack is something we had not foreseen, we do not want this to affect our users in any negative way. Expect a plan released in 48 hours.
— Belt Finance (@BELT_Finance) May 30, 2021















