This article explains what frontrunning is, how it negatively affects the DeFi sector, and what you can do to avoid getting your DEX transactions frontrun.
What is frontrunning?
Whenever you use a decentralized exchange to swap tokens, the price of the token you buy increases slightly. This is called slippage and for most retail traders, slippage is barely even noticeable. Whale traders however, especially when they purchase highly illiquid tokens, can significantly change a token’s price.
Frontrunning bots take advantage of this mechanic by beating out the trader on the gas fees, purchasing into a token at the lower price and then instantly selling them off at the higher price. In a block explorer, frontruns leave a clear trace with the trader’s transaction being “sandwiched” between the two frontrun transactions.
This YouTube video shows the potential profits frontrunners can expect at the expense of DEX users. One of these sandwich attacks had the frontrunner invest a little less than 7,500 USD to come up with a 1,500 USD profit.
Is frontrunning illegal?
Frontrunning is not exclusively known to crypto assets. For example, the Payment for Order Flow business model used by many retail stock trading apps such as Robinhood has been criticised for potentially allowing frontruns.
Using insider information to frontrun stock trades is definitely illegal. In 2020, Robinhood paid a 65 million USD fine after the SEC found that the trading app sold client orders to high-speed trading firms.
In crypto however, all pending trades are published openly in the mempool, so everyone has the information that a large trade will take place. Therefore, frontrunning DEX trades does not constitute insider trading.
So far, no legal prosecution of crypto frontrunners has ever been attempted. Since it is such a common occurrence, even the crypto community is split on whether frontrunning should be considered an exploit, or just part and parcel of decentralized finance. The practice is deemed immoral though by most members of the crypto community.
How to avoid getting frontrun
As noted above, illiquid tokens are most at risk of frontruns, since they are more prone to slippage. Therefore, extra caution should be applied when trading these tokens.
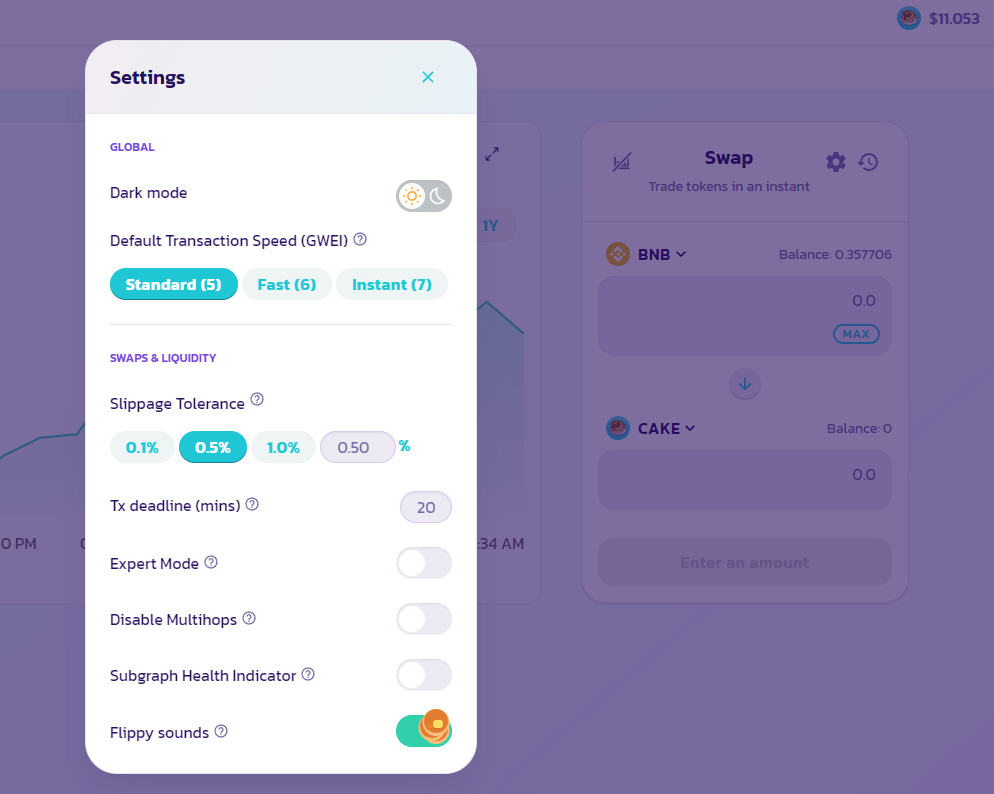
Most DEXes warn the user if a high slippage is to be expected on a trade, ultimately rejecting the transaction if a certain threshold is exceeded. To be on the safe side, don’t increase the slippage tolerance above 0.5% when executing a large trade.
Keep in mind that frontrunners have to use twice the gas fee of a normal trader for a sandwich attack. It therefore is typically cheaper to split up large trades into two or more smaller trades and pay the gas fees than paying the gas fees only once, but risk getting frontrun.
Another option is to increase the gas fee when confirming the transaction in your wallet. On faster blockchains such as Binance Smart Chain, increasing the fee by just one Gwei is typically enough to ensure that the transaction gets included in the next block. Since the activation of EIP-1559, the extra costs of fast block inclusion have also decreased to a minimum on Ethereum.
Crypto’s most elaborate scam
Most scams in crypto are typically low-effort attempts to convince gullible and less experienced crypto users into sending funds to the scammers address or DApp. Here is an example of a highly elaborated scam that specifically targets advanced users.
Recently, several YouTube videos have popped up that claim to be tutorials for setting up frontrunning bots. These videos advise users to deploy and fund a smart contract, which will supposedly carry out frontruns, with their MetaMask wallet.
https://www.youtube.com/watch?v=apUu_uD9a-8
WARNING: This is a confirmed scam. Do not execute and fund the smart contract shown in this video.
Surprisingly, while appealing to the same greed as the usual get-rich-quick schemes, these scammers actually tell a convincing story and the promised returns are somewhat in line with what an actual frontrunning bot could expect. In the video above, the scammer actually puts in the extra effort of curating and replying to comments, however most commenters can be quickly identified as new YouTube accounts.
Also, being able to use a smart contract for frontrunning is implausible, since smart contracts cannot access the mempool, thus having no information about pending trades. Analysis of the smart contract shows that most of the code lines are commented out.
Also, the contract imports another smart contract from IPFS, which is suspicious. This secondary contract also has most lines commented out, but one line that is not commented out points at the BSC address 0xbFf0F5A27dfCed442f11e9dcEA019ce3f23da0b0.
Inspection of this address within a block explorer reveals that it receives regular inflows of little more than 0.4 BNB, which is what the scammer advises as the minimum funding amount. The scammer’s wallet shows a balance of about 20,000 USD. Most recently, the scammer cashed out 20 BNB (~9,600 USD) using the anonymizer Tornado Cash.
This video by Blocksherpa explains how smart contracts can be analyzed for a possible scam, using another video that advertised a fake frontrunning bot. Interestingly, the video he is referring to merely recites the scam video above word by word, but is read by someone with a clearly different voice. Apparently, this scam method has already attracted copycats.















